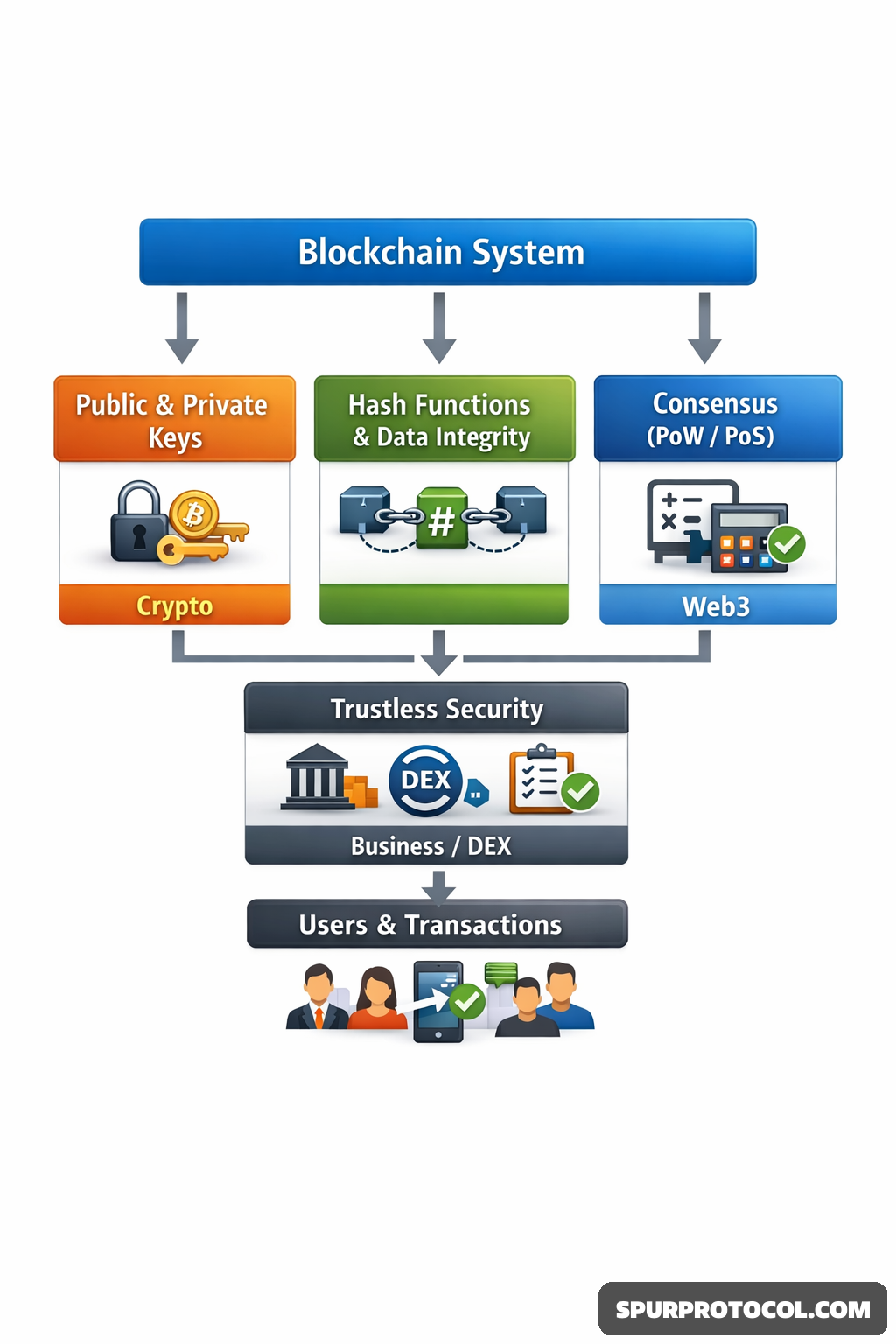
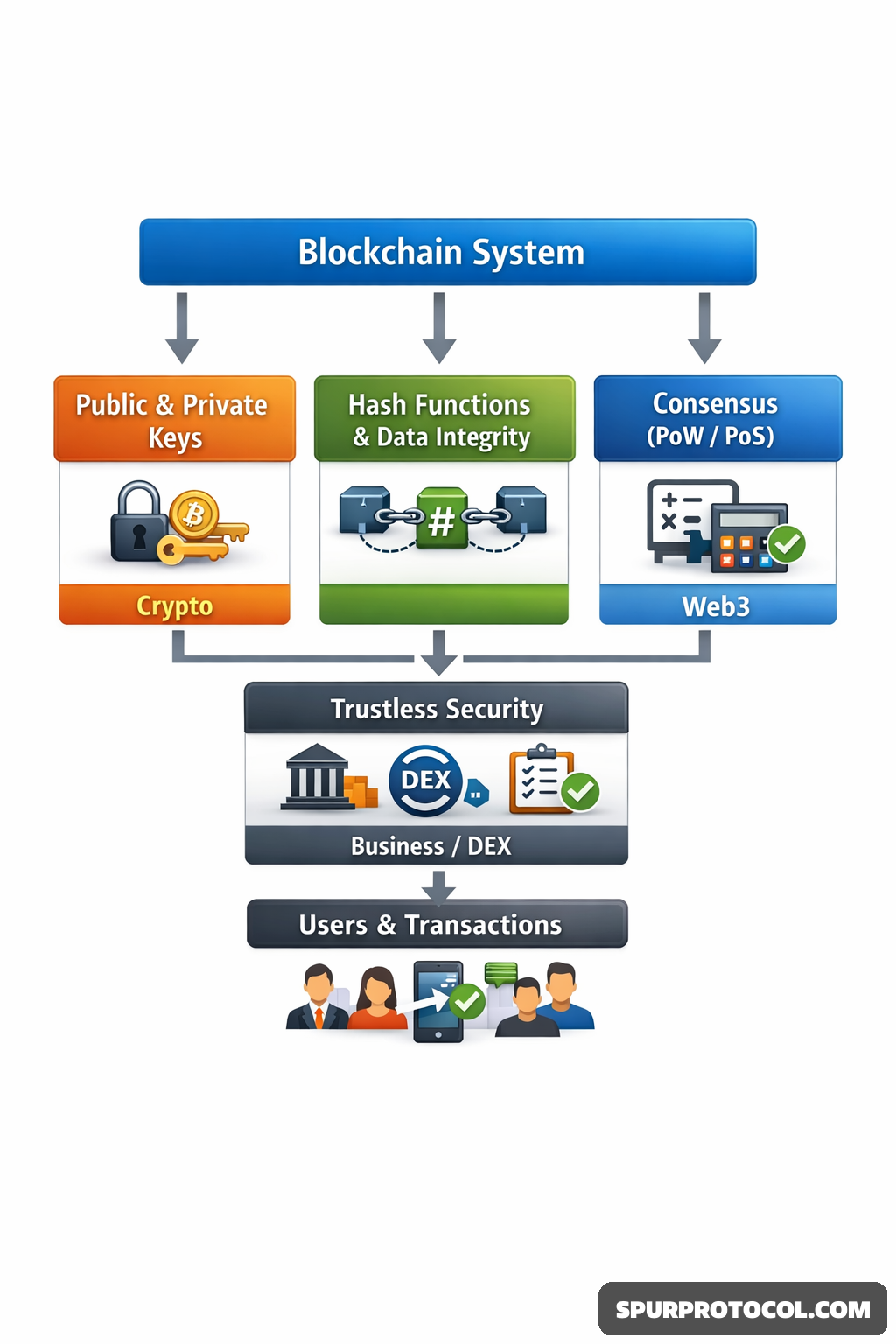
How Cryptography Ensures The Security Of Blockchain Systems
Blockchains are called secure by design, but that’s no accident. At their core is cryptography – the math that protects transactions, proves ownership, and keeps trust without a central authority. It’s what makes blockchains tough to hack or tamper with.
Go Back
🕒 1:46 PM
📅 Feb 24, 2026
✍️ By Goko7
Public and Private Keys: The Foundation of Ownership
A key part of blockchain security is public-key cryptography. Each user has a pair of keys: a public key, like an address, and a private key, like a secret password. Transactions are signed with the private key, proving ownership without revealing it. The network can verify the signature with the public key, ensuring authenticity and preventing unauthorized spending.
Hash Functions and Data Integrity
Cryptographic hash functions convert data into a fixed-length string. Even a tiny change in the original data produces a completely different hash. Each block contains the hash of the previous block, forming a continuous chain. Altering a past transaction changes the hash, breaks the chain, and alerts the network, making blockchains highly resistant to tampering.
Consensus and Security Through Mathematics
Beyond keys and hashes, cryptography enables consensus mechanisms like proof-of-work or proof-of-stake. These mathematical rules ensure all participants agree on a single version of the ledger. Distributed verification makes attacking the network computationally difficult.
A System Built on Trustless Security
Blockchains operate without relying on a central authority. Trust comes from transparent algorithms and mathematical proofs. While no system is completely risk-free, cryptography forms the foundation that keeps blockchain networks secure, reliable, and resistant to fraud.