Stealth Addresses And Privacy
What you should know about Stealth Addresses and Privacy
Go Back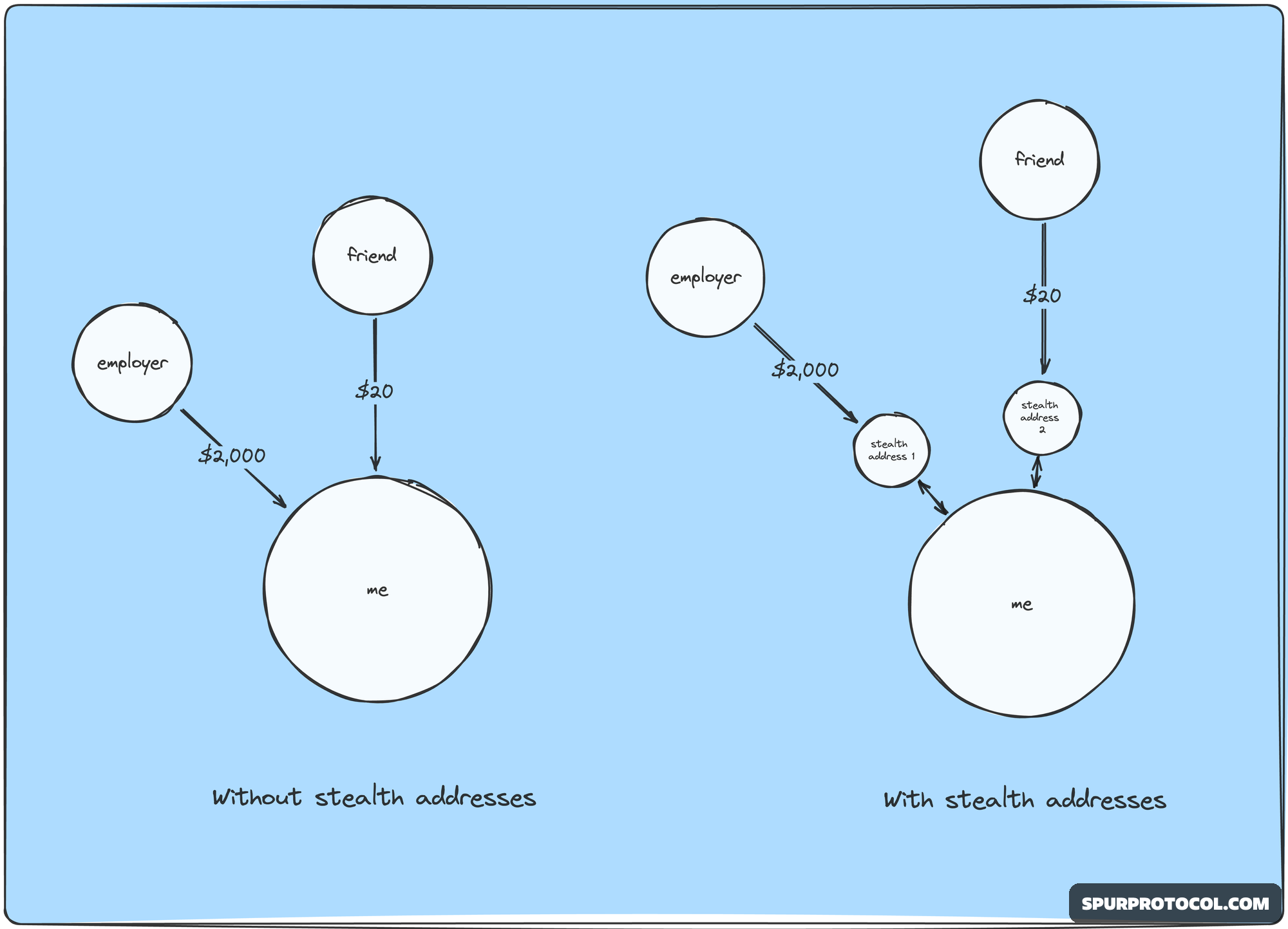
🕒 9:36 AM
📅 Mar 30, 2025
✍️ By KingWasberryBest
What you should know about Stealth Addresses and Privacy
Go Back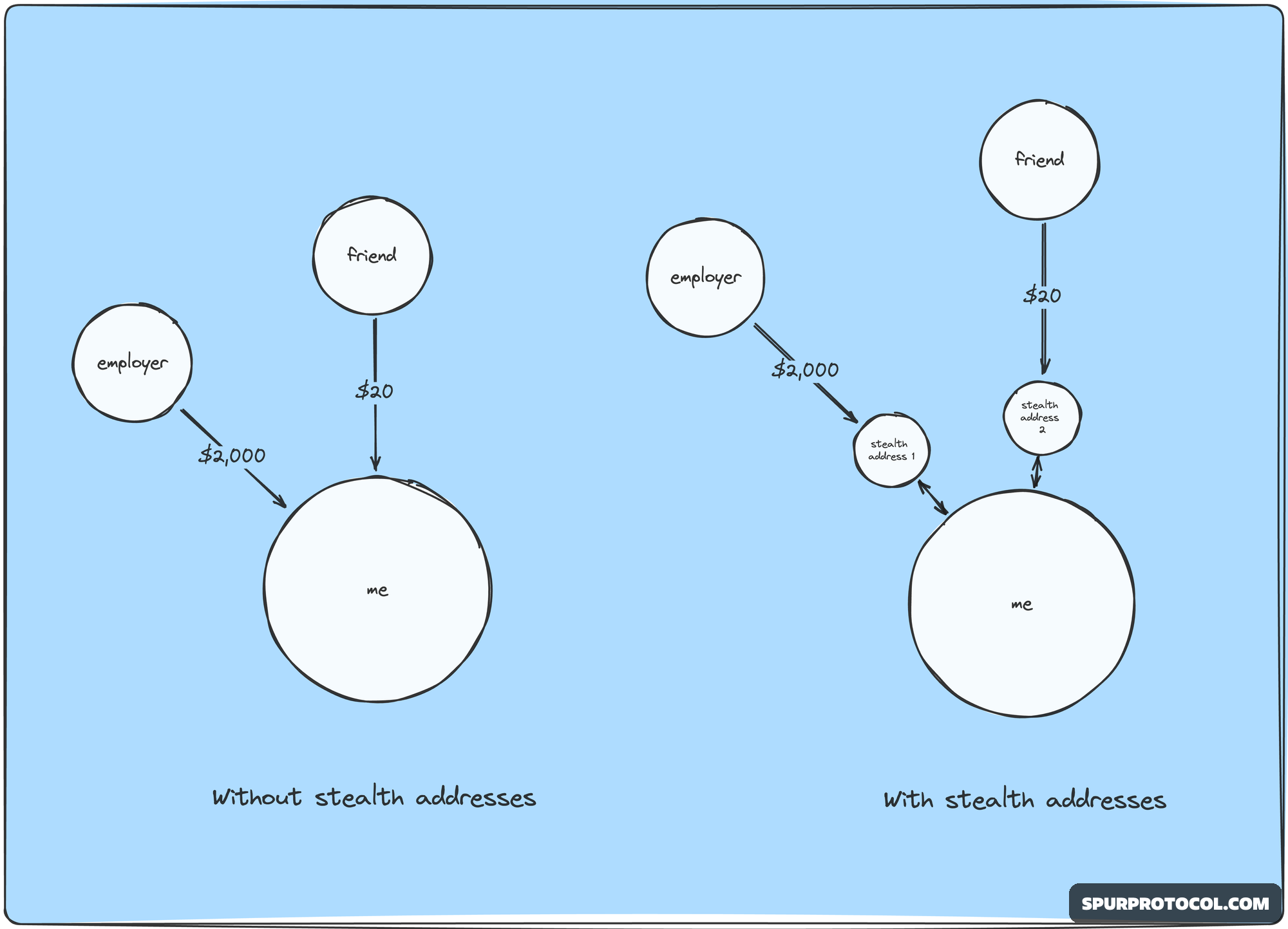
🕒 9:36 AM
📅 Mar 30, 2025
✍️ By KingWasberryBest
Stealth addresses are a cryptographic technique used to enhance privacy in cryptocurrency transactions. Here's how they work:
What are Stealth Addresses?
1.Definition: Stealth addresses are a type of cryptographic address that allows users to receive cryptocurrency payments without revealing their actual address.
2.Purpose: Stealth addresses aim to enhance user privacy by making it difficult for outsiders to track transactions and link them to the recipient's identity.
How do Stealth Addresses Work?
1.Ephemeral Address Generation: When a user wants to receive a payment, they generate a new, ephemeral address using a cryptographic algorithm.
2.One-Time Use: This ephemeral address is used only once and then discarded.
3.Unlinkability: The ephemeral address is designed to be unlinkable to the user's actual address or identity.
Benefits of Stealth Addresses
1.Improved Privacy: Stealth addresses make it difficult for outsiders to track transactions and link them to the recipient's identity.
2.Enhanced Security: By using a new, ephemeral address for each transaction, users reduce the risk of address reuse and associated security vulnerabilities.
3.Increased Anonymity: Stealth addresses help users maintain anonymity when receiving cryptocurrency payments.
Implementations of Stealth Addresses
1.Monero: Monero, a privacy-focused cryptocurrency, uses stealth addresses to enhance user privacy.
2.Zcash: Zcash, another privacy-focused cryptocurrency, uses a variant of stealth addresses called "shielded addresses."
3.Other Cryptocurrencies: Other cryptocurrencies, such as Bitcoin and Ethereum, are exploring the implementation of stealth addresses or similar privacy-enhancing technologies.
Challenges and Limitations
1.Scalability: Stealth addresses can increase transaction complexity, which can impact scalability.
2.Regulatory Compliance: Stealth addresses may raise regulatory concerns, as they can be used to facilitate illicit activities.
3.User Adoption: Widespread adoption of stealth addresses may be hindered by the need for users to understand and manage complex cryptographic techniques.
Future of Stealth Addresses
1.Advancements in Cryptography: Ongoing advancements in cryptography may lead to more efficient and user-friendly stealth address implementations.
2.Increased Adoption: Growing demand for privacy-enhancing technologies may drive increased adoption of stealth addresses in various cryptocurrencies.
3.Regulatory Clarity: Clearer regulatory guidelines may help alleviate concerns and facilitate the development of stealth address technologies.